Website Security Guide
Quick Sprout
AUGUST 8, 2023
We’re not saying this to try and scare you, but that’s the reality of the … Website Security Guide Read More » The post Website Security Guide appeared first on. Your website is at risk.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 security
security 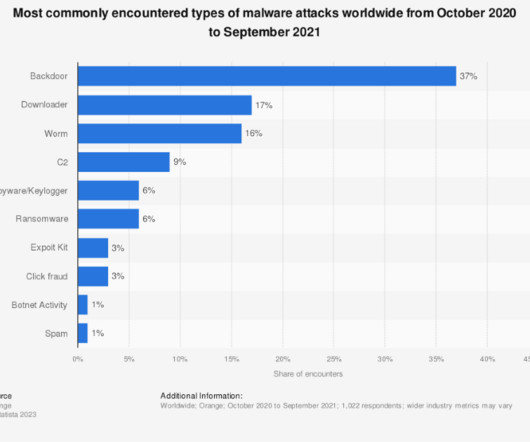
Quick Sprout
AUGUST 8, 2023
We’re not saying this to try and scare you, but that’s the reality of the … Website Security Guide Read More » The post Website Security Guide appeared first on. Your website is at risk.
Quick Sprout
AUGUST 7, 2023
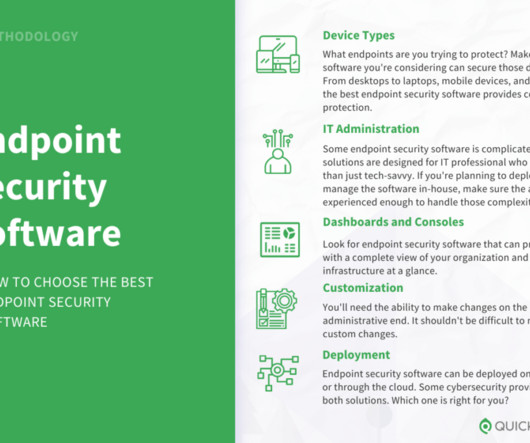
The best endpoint security software for most people is Bitdefender or Avast Business … Compare The Best Endpoint Security Software Read More » The post Compare The Best Endpoint Security Software appeared first on. Want to jump straight to the answer?
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Quick Sprout
AUGUST 22, 2023
Don’t assume your … WordPress Security Beginner’s Guide Read More » The post WordPress Security Beginner’s Guide appeared first on. As the world’s most popular CMS, WordPress websites are a vulnerable target for hackers and scammers worldwide.

Grammarly
DECEMBER 19, 2022
Written by Suha Can, Chief Information Security Officer at Grammarly. At Grammarly, providing best-in-class writing support also means ensuring best-in-class security. A big part of our security-first mindset is maintaining internal safeguards—including programs and testing to identify and resolve issues before any occur.
Jasper
SEPTEMBER 20, 2023
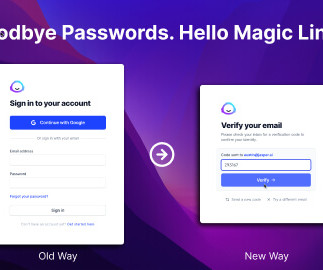
This new way to login Jasper is faster, more secure, and you'll never have to remember a password again. Introducing Magic Link Logins.

Quick Sprout
SEPTEMBER 6, 2023
… SFTP: How to Transfer Files Securely the First Time Read More » The post SFTP: How to Transfer Files Securely the First Time appeared first on. Data transfer is a typical operation in daily digital life, and SFTP is an essential tool for transferring sensitive information.

Neil Patel
MAY 10, 2021
Blockchain technology is a new way to secure your data. ” The blocks of information are bound and secured together by cryptographic principles called chains. How Does Blockchain Work for Data Security? Why Should You Use Blockchain in Marketing Data Security? Blockchain Improves Security, Encryption, and Validation.

Blogtrepreneur
NOVEMBER 11, 2022
A career in homeland security is for mission-oriented individuals with a passion for serving their country. Although national protection doesn’t fall under the purview of any one department or tier of government, the department of homeland security is largely responsible for safeguarding the nation from all threats.

Spectrum Net Designs
SEPTEMBER 2, 2022
Why is Website Security So Important? As technology continues to change, the challenge for businesses to keep their personal and customer’s information on the web secure continues to increase. Web security is extremely important because it keeps hackers and cyber-thieves from accessing sensitive information.

Freelance Union
AUGUST 7, 2023
In 2020 the SECURE Act 2.0 Here are some key provisions that freelance business owners should be aware of regarding the SECURE 2.0 Roth options are available for SIMPLE & SEP IRAs through the SECURE 2.0 Before SECURE Act 2.0, SIMPLE IRA employer contributions are also increased under the SECURE 2.0

DienyeDiri.Com
MARCH 25, 2024
The post Stanhope Secures £2.3m But it’s not just them – Creator Fund, MMC Ventures, […] The post Stanhope Secures £2.3m They managed to raise £2.3 million in funding, and the UCL Technology Fund was a big part of it. They managed to raise £2.3 million in funding, and the UCL Technology Fund was a big part of it.

Smart Blogger
JULY 25, 2023
If you’re not using a whitelist to secure your emails, you’ve probably already made it onto this year’s hit list for hackers and cybercriminals. Add their specific email address to your whitelist, and they’ll get VIP access to your inbox without waiting in line for a security check. How do we know this? Luckily, we’ve got you covered.

Blogtrepreneur
NOVEMBER 17, 2022
The study evaluates each risk to your firm’s data, devices, and information security and ranks the potential dangers. However, every firm must customise its strategy to manage those particular risks inside its risk management processes, because every organisation has a distinct set of security concerns. Cybersecurity. Conclusion.

Grammarly
APRIL 3, 2023
During a Grammarly-hosted panel at SXSW, AI experts discussed the implications of generative AI from a security and user trust perspective as well as the importance of responsible AI development. The speed at which this took place means that they may not have enterprise-grade security practices in place,” Can said.

AWAI
JULY 28, 2023
The only way to achieve TRUE financial security is to control your income. A perfect place to start is becoming a part of our Barefoot Writer Club.
Grammarly
JANUARY 23, 2023
Thus, we were able to develop a practical solution that gives us the best security possible: Critical apps and SaaS authenticate via FIDO2 only; everything else authenticates via FIDO2 if it’s supported and falls back to using OTP/push. For instance, YubiKeys combine several security interfaces. ” followed by the Enter key.

BKA Content
OCTOBER 10, 2022
How To Prepare for a Recession: Securing Longevity Through Proactive Decision-Making. The post How To Prepare for a Recession: Securing Longevity Through Proactive Decision-Making appeared first on BKA Content. Collaboration Corner. Commonly Confused Words. Figures of Speech. Writing Tips. Miscellaneous. Write for BKA.

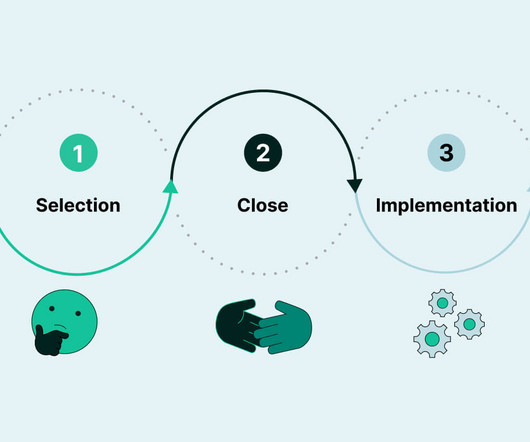
Content Marketing Institute
MAY 16, 2022
When it comes to cyber safety, the protective measures your CMS takes can mean the difference between a seamless customer experience and serious breaches of trust. Let’s explore how to select CMS tech with greater confidence. Continue reading →

Freelance Union
APRIL 24, 2024
With taxpayers continuing to be bombarded by email and text scams, the IRS and the Security Summit partners warned individuals and businesses to remain vigilant against these attacks. The Federal Communications Commission's Smartphone Security Checker is a useful tool against mobile security threats.

Blogtrepreneur
NOVEMBER 16, 2023
This transaction data is encrypted by the payment gateway, ensuring it remains secure. Each type caters to different business needs and customer preferences: Hosted Payment Gateways : Hosted payment gateways take customers to a secure payment page managed by the gateway provider. It sends this encrypted data to the payment processor.

Blogtrepreneur
FEBRUARY 9, 2024
But how can you secure the business name effectively? Apply for Trademarks Securing trademarks is crucial to protect your brand’s identity. Secure a Domain Name In today’s digital age, securing an online presence is indispensable. It all begins with choosing the right business name.
Blogtrepreneur
DECEMBER 30, 2023
For example, when sending large, bulky imaging equipment , you’ll need wheeled trolleys with belts or ropes to secure it in place. When delivering vials of blood to the local hospital laboratory for analysis, you may need temperature-controlled, secure packaging.

Grammarly
DECEMBER 19, 2022
The three discussed building a streamlined vendor ecosystem that emphasizes employee engagement and impact while balancing security. . Ensure your corporate infrastructure enables employee access to WPX tools remotely without sacrificing security . Evaluate WPX vendors with an eye toward simplifying to drive impact.

The Hoth
NOVEMBER 2, 2023
Besides the padlock, the URL will also begin with ‘https,’ which is how you know your connection is secure. If there’s no padlock and you see ‘http,’ your connection isn’t secure. Here’s a quick breakdown of each term: SSL (Secure Socket Layer). It can also securely connect two servers. TLS (Transport Layer Security).

Freelance Magic
JANUARY 16, 2024
Identify recently funded companies Companies that have recently secured funding are often in a position to invest in new projects and services. By tailoring outreach efforts to these key figures, you can increase your chances of securing bigger, better projects.
Freelance Union
OCTOBER 16, 2023
Why your home Wi-Fi network security is so important Public Wi-Fi networks are dangerous — that hardly surprises anyone today. Domestic Wi-Fi networks, on the other hand, are thought to be as secure as safe deposit boxes. Another security gap is unreliable network encryption. Second, configure your port security.
Freelance Writing Jobs
APRIL 10, 2024
This article details why learning to convert DOCX files to PDF is not just a technical necessity but a strategic move toward ensuring your work retains its formatting, remains secure, and becomes universally accessible across platforms. Enhanced security. Even a regular web browser can open PDF docs with no trouble.
Grammarly
JANUARY 9, 2024
In this post, we’ll share how our vulnerability management program at Grammarly keeps our development pipeline and user data secure. Previously, like many other companies, we relied on several vulnerability platforms to automate our security assessments. Work on what matters” is one of our most important tenets as a security team.

Grammarly
OCTOBER 12, 2023
Being Chief Information Security Officer comes with a lot of responsibility. I call these nightmare-level threats the Four Horsemen of Generative AI: Security Vulnerabilities, Third Party Risk, Privacy and Copyright, and Output Quality. A secure perimeter means nothing if you leave the locks open. Do your due diligence.

Jasper
JUNE 26, 2023
What you need to know about the current state of user data protection in AI tools.

ProBlogger
AUGUST 28, 2012
This guest post is by Anders Vinther of The WordPress Security Checklist. WordPress Security is about as sexy as cleaning your house. And as a serious blogger, you already know that securing your site properly is not a trivial task. Here are the myths: WordPress is not secure. My WordPress site is 100% secure.
Grammarly
OCTOBER 20, 2023
The Framework for Safe Generative AI Adoption Grammarly has over 14 years of experience developing and providing secure, private, and responsible AI. Rather than companies attempting to block the use of AI, Suha recommends following a strategic approach for adopting generative AI safely, based on his own recent experience at Grammarly.
ProBlogger
JANUARY 7, 2013
This guest post is by Anders Vinther of The WordPress Security Checklist. And there is no better time to review the security plugins you use on your WordPress site. Last year important new security plugins were released, and some of the existing plugins were updated. WP Login Security 2. Instructions: WP Login Security 2.

Freelance Union
JANUARY 30, 2024
Understanding the basics of coding can help you customize sites to fit your unique vision and troubleshoot common issues, empowering you to take control of a website's look, feel, functionality, and security. The majority of these security breaches (44%!) Due to its popularity, WordPress is a prime target for hackers.

Freelance Union
OCTOBER 19, 2023
Traditionally, these toolsets have been designed toward corporations as the primary ‘customer’ Because of this, many freelancers today still struggle with providing proof of income for key financial transactions and securing affordable yet premium benefits like health insurance and group 401K.

Blogtrepreneur
MARCH 20, 2024
Social security tax comprehension and management is an additional critical element of tax planning for independent contractors. In contrast to traditional employees, freelancers are obligated to pay both the employer and employee contributions towards their social security taxes, which are not routinely deducted from their wages.

Jane Friedman
FEBRUARY 19, 2024
Enter the Circle of Security, a parenting model I encountered during graduate school. The Circle of Security was created by Robert Marvin, Glen Cooper, Kent Hoffman, and Bert Powell to help parents attend to their child’s needs as they learn to explore the world. Build a secure process Your first task is to choose a process to follow.
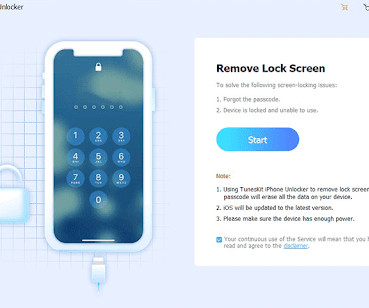
Blogtrepreneur
MARCH 27, 2024
With identity theft and cyber-attacks on the rise, setting a strong passcode adds an extra layer of security to prevent sensitive information from falling into the wrong hands. In addition to security benefits, having a passcode enables features like Touch ID and Face ID for convenient and quick access to your device.
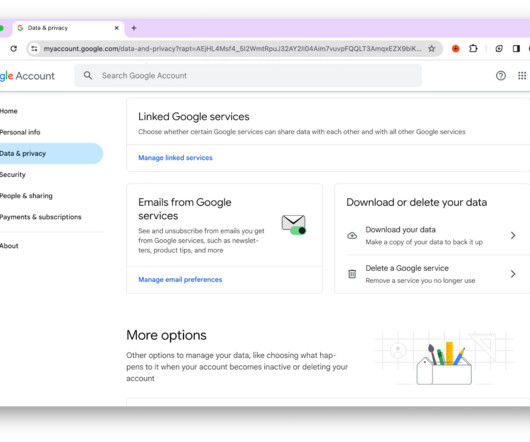
Freelance Union
FEBRUARY 14, 2024
Afterward, you can follow up with a detailed security audit of your Gmail account. " Click on Security in the side menu of the screen. You get sudden security notifications A sudden "Did you just sign in?" It will take you to a new page where you can post your questions and get in touch with a Gmail Security expert.
Blogtrepreneur
JANUARY 25, 2024
By adopting simple yet effective strategies, individuals can make their money work for them, paving the way for a secure financial future. By embracing these simple yet impactful strategies, individuals can take charge of their financial destinies and cultivate a future of stability, security, and prosperity.
Quick Sprout
FEBRUARY 1, 2023
And although the fax machine now has its place in technological nostalgia, the need to send documents securely over the internet remains. Faxes are still the go-to method of sending important documents quickly and securely. Security: Online faxing is a secure and reliable way to send documents online.

Article Writing
SEPTEMBER 21, 2023
This guide will dig deep into guest posts and explain precisely what you need to know to secure them and share content across the internet in a reliable and repeatable process. This is probably one of the easiest ways to secure a guest post. The post Ultimate Guide to Secure a Guest Post Anywhere – Every Time!

Grammarly
MARCH 19, 2024
Learn More About Enterprise-Grade AI Find out how your IT team can move faster and drive greater results with trustworthy, secure, private, and responsible enterprise-grade AI. Contact Sales Note: all hours referenced have been rounded to the nearest whole number.

ProBlogger
MAY 27, 2012
But we don’t have to know how hijacking a domain or stealing a blog works to be able to implement some basic security precautions. And that is exactly what this post is about—making your blog secure without playing with source code, understanding things, and stuff. Typical WordPress security problems. Hosting security.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content